IT@JH is disabling external AI meeting assistantsLearn How to Help
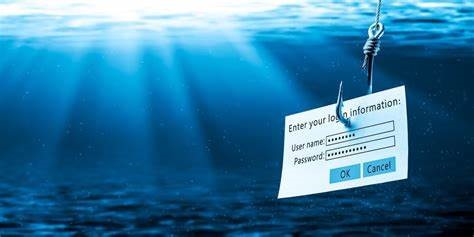
Phishing (pronounced “fishing”) is a form of identity theft that attempts to trick people into revealing personal or financial information online. Phishing scam attackers use phony websites or email messages that appear to be from trusted businesses and brands in order to steal personal information such as usernames, passwords, credit card numbers, or Social Security numbers.
The perpetrator may also send an email message that contains malicious files, often Word, Excel, or PDF documents. These malicious files can install worms or viruses on your computer. They can also install malicious software called “ransomware” intended to prevent you from accessing your computer’s files. Once the files are locked, the attacker demands a ransom, generally monetary, to unlock them.
For more information, check phishing.jh.edu (for internal users only). Johns Hopkins users should send suspicious and/or spam emails as an attachment to [email protected].